Small—to mid-sized organizations are now among cybercriminals’ most prominent targets. Cyberattacks come in all shapes and sizes, with one goal: to steal your data or financial information. This information is often resold on the dark web.
Cybercriminals use malware as their most frequently used cyberattack method. According to Statista Research, the number of malware attacks reached 2.8 billion during the first half of 2022.
This number has surged, especially after the pandemic, as remote work environments have increased security vulnerabilities. Simultaneously, hackers are becoming an industry as they grow more sophisticated and organized daily. As a result, experts estimate that cybercrime will cost businesses $10.5 trillion annually by 2025.
This article will explore malware, the eight most common attacks, and the best prevention methods.
What Are Malware Attacks?
Malware may be one of your company’s most significant threats as it enters your systems most simply and innocently.
Malware is an umbrella term that describes and includes any malicious code or program harmful to an organization’s system. Its goal is to damage, invade, and turn off networks, computers, tablets, and mobile devices by taking partial control over the operating system.
A malware attack is a cyberattack where this malicious software is used to infiltrate a computer system, causing damage or unauthorized access to data without the user’s knowledge, stealing sensitive information, disrupting operations, or extorting money from the victim. Some common examples of malware include viruses, ransomware, spyware, and worms. Malware is designed with a malicious intent to harm a system or steal data, unlike regular software, which is meant to perform a specific function.
What is commonly referred to as malware is malicious software that is:
- Attached to emails
- Embedded in spam, fraudulent links
- Found on various sites that your employees or executives visit online.
Once it’s entered your system, the malware exploits computers and networks to steal money or data. All it takes is one click on the wrong website or link for the malware to install itself on a device and start its program.
Malware is typically designed to steal:
- Passwords
- Data
- Financial information
- Trade secrets
- Company information, etc.
Various types of malware spread and steal information differently.
Here are some common ways malware spreads:
- Phishing emails: Cybercriminals use email addresses to trick users into opening malicious attachments
- Infected websites: Users can download malware from websites that have been compromised
- Malvertising: Users can be tricked into installing malware through malicious advertisements on popular sites
- USB drives: Malware can be spread through USB drives that have been infected, or it can exploit vulnerabilities in software or operating systems. Sometimes, users even download malware from compromised websites.
- Social engineering: Users can be tricked into downloading malware through social network spam, or cybercriminals can trick users into downloading malware through man-in-the-middle attacks.
- Peer-to-peer file-sharing: It happens when malware spreads through peer-to-peer file-sharing networks
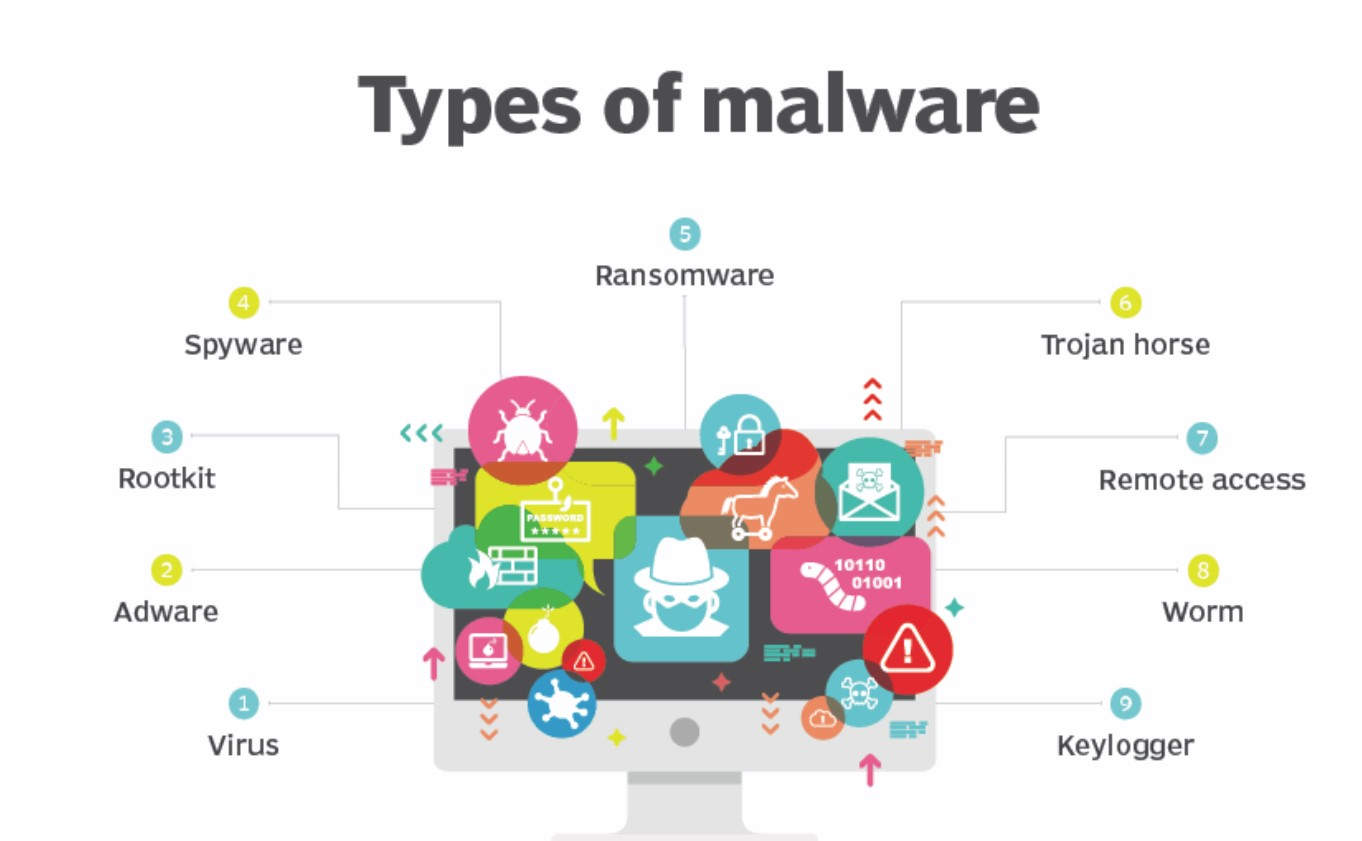
What are the 8 Most Common Types of Malware Attacks?
Here’s a list of the most common types of malware attacks.
1. Adware
Adware is malware that displays unwanted or malicious advertising. This type of malware is relatively harmless but can be highly irritating as spammy ads keep popping up repeatedly. Additionally, these ads can cause many users to download harmful malware on their devices.
You can defend your system against adware by updating your web browser, operating system, and email lists. Taking these measures will enable your system to block adware attacks before they can download and install malware on your system.
2. Fileless Malware
Fileless malware doesn’t directly affect files or the file system, unlike classical malware, which infects machines through executable files.
Instead, this malware infects your computer using non-file objects like PowerShell, WMI, Microsoft Office macros, and other system features.
Early examples of malware attacks include Frodo, Number of the Beast, and the Dark Avenger. Recently, this malware was used to attack the Democratic National Committee and cause the Equifax breach.
3. Viruses
A virus is malware that infects other programs and can spread from one system to another. Once the virus file is launched, it encrypts, deletes, and corrupts your system data and files.
Installing a trusted and advanced antivirus allows you to secure and protect all your devices from a single location while ensuring control and visibility. Scan your computers regularly and update your antivirus software when required.
4. Trojans
Much like the famous Trojan Horse, which fooled the inhabitants of Troy during the epic Greek war, trojan malware pretends to be an actual program and tricks users into installing it on their systems.
Trojan malware has to be run by its victim to spread from one device to another. Typically, a trojan enters your network via email or is distributed to users via a website link. Trojans can be more challenging to eliminate since they rely on social engineering to spread and download.
The most straightforward approach to protect yourself from trojans is never downloading or installing software from an untrusted source. Instead, ensure that your staff downloads apps only from trusted app shops and pre-approved developers.
5. Worms
Worms count among the types of malware that spread to several devices or systems, just like a virus. Yet, a worm differs from a virus in one crucial aspect. Worms are standalone programs that replicate themselves to infect other computers.
A worm, however, does not spread to other programs. This type of malware frequently targets well-known exploits. So, ensure that every device in your network has the most recent fixes installed to defend yourself against worms.
You can also find suspicious files or links that might contain a worm using firewalls and email filters.
6. Bots
A bot is a specially created software program designed to perform the same action on repeat without any external interference. A system with a bot infection can infect an entire network, creating what is called a botnet.
Using the botnet, hackers can use your entire network of systems to launch massive attacks. Meanwhile, the users of these systems are unaware of how their devices are being used.
Bots can launch large attacks that can bring down entire companies or countries, making these types of malware attacks particularly dangerous.
7. Ransomware
Ransomware encrypts a victim’s files and demands payment in exchange for decryption. Hackers may still delete or expose data even if a ransom is paid.
Ransomware assaults make the news regularly due to their impact on governmental agencies, telecommunications companies, railroad networks, and hospitals. The WannaCry attack in May 2017 shut down systems across 150 countries, infecting over 200,000 devices. As hackers work together to pull off bigger heists, ransomware attacks will keep increasing.
The best way to combat these malware attacks is to create routine backups at a secure off-site facility. You should also train your staff on cyber hygiene best practices to prevent people from clicking on harmful links.
8. Spyware
The spyware can access user names, passwords, and personal information by recording the user’s keystrokes over a day.
Antivirus software can help you find and remove spyware like other types of malware. By employing anti-tracking browser extensions, you can also stop spyware from following your users from site to site.
How to Tell If Your System Is Infected with Malware
Warning signs of malware infection include:
- Sluggish performance or system crashes
- Unwanted pop-ups and browser redirects
- Unusual login attempts on online accounts
- Unexpected files, messages, or app installations
- Disabled antivirus software
If you notice these symptoms, run a malware scan immediately and follow security best practices to mitigate further damage.
Impact of Malware on Businesses
- Data Theft and Financial Loss: Malware can steal confidential data and lead to significant financial losses.
- Operational Downtime: Ransomware or system crashes can halt business operations.
- Legal and Compliance Risks: Data breaches can result in fines, lawsuits, and loss of customer trust.
Best Practices for Prevention Against Malware Attacks
Here are some practical ways to prevent malware attacks:
- Install Antivirus & Endpoint Protection
- Enable Software & System Updates
- Use Multi-Factor Authentication (MFA)
- Train Employees on Phishing & Cyber Hygiene
- Secure Backups in an Offsite Location
What to Do After a Malware Attack
Here are the steps you should take after a malware attack:
- Isolate the Infected Device: Disconnect the affected computer or device from the network to prevent the malware from spreading.
- Contact Your IT Support: If you have access to IT support, inform them immediately about the malware attack.
- Run a Full System Scan: Use reputable antivirus software to scan your system for malware and remove any detected threats.
- Update Your Security Software: Ensure your antivirus software is updated to the latest version with the most recent malware definitions.
- Restore From Backups: If your data has been compromised, attempt to restore it from a clean backup.
- Change Passwords: Change all passwords for important online accounts that the malware may have accessed.
- Review Recent Activity: Check your online banking statements and other sensitive accounts for suspicious activity.
- Review Browser Extensions: Remove any suspicious browser extensions the malware may have installed.
- Consider a System Restore: Depending on the severity of the attack, you may need to restore the system to a clean state.
- Report the Attack: If you believe the attack was particularly serious or involved sensitive data, consider reporting the incident to relevant authorities.
Prevent Malware Attacks with Imagine IT
Cybercriminals constantly evolve their tactics, making malware attacks a persistent threat. Without strong cybersecurity measures, your business remains vulnerable to these malicious threats.
At Imagine IT, we provide managed cyber security service to safeguard businesses against evolving cyber threats. As a trusted name for managed services in Garden City, Sterling, Zeeland, Bloomington, and Wichita, we offer advanced security solutions, continuous monitoring, and proactive threat management. Contact Imagine IT today to safeguard your organization against cyber threats.